8 Powerful Kerberos attacks (that analysts hate)
Discover the most common Kerberos attacks that every red teamer should know (and analysts fear), and learn how to execute them with real-world examples.
Table of Contents
This post is based on the Hack The Box (HTB) Academy module (or course) on Kerberos Attacks. The module provides an in-depth study of the Kerberos protocol and its authentication process within an Active Directory network
You can learn more by browsing the catalog of free or advanced cybersecurity courses on the HTB Academy!
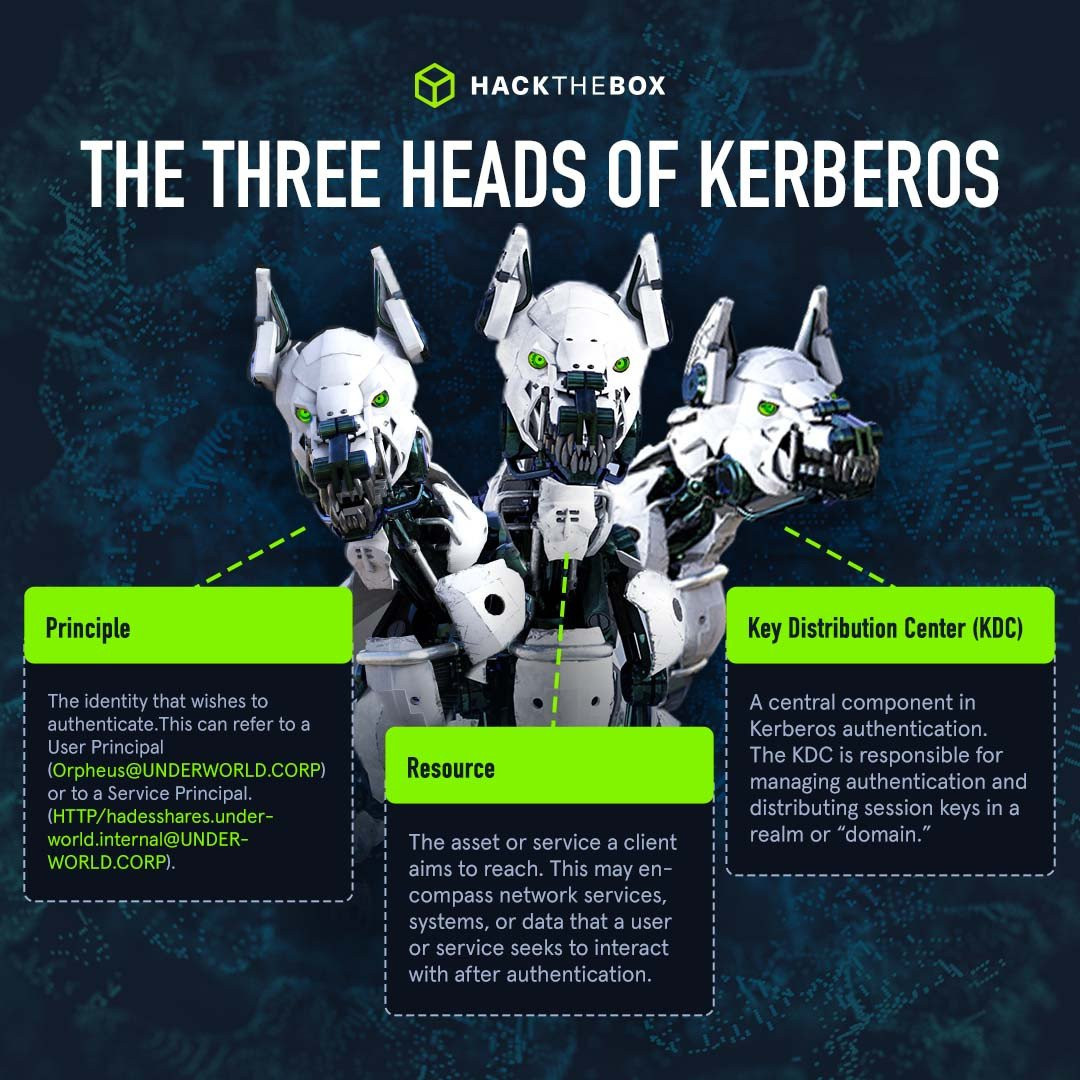
What is Kerberos?
Kerberos is a protocol that allows users to authenticate on the network and then access services.
When a user logs into their PC, Kerberos is used to authenticate them. It is used whenever a user wants to access a service on the network.
Thanks to Kerberos, a user doesn't need to type their password in constantly, and the server won't need to know every user's password. This is an example of centralized authentication.
Kerberos is a stateless authentication protocol based on tickets. It effectively separates a user's credentials from their requests to resources, ensuring their password is not transmitted over the network.
Is Kerberos a vulnerable authentication protocol?
In this post, we’re focusing on how to attack and infiltrate Kerberos authentification, which may lead you to believe that it’s a weak protocol. However, before Kerberos, authentication resulted in a user's hash stored within memory upon authentication.
If a target machine was compromised and the hash was stolen, the attacker could access anything that the user account had access to via a Pass-The-Hash attack.
With Kerberos authentication, credentials must be specific for every machine they want to access because there is no password. This means that the attacker is limited to the resources that the victim user authenticated against.
Kerberos is considered one of the most secure and robust authentication mechanisms out there. Although no security measure is completely invulnerable, and Kerberos is no exception.
Learn Kerberos attacks with Academy

-
Interactive module on the most common Kerberos attacks: roasting, delegation, and ticket abuse.
-
Learn how to harden, mitigate, and detect Kerberos attacks, boosting your security knowledge base.
-
Finish the course with a practical hands-on skills assessment to test your newly developed skills.
Note💡: Read our detailed (and visual) Kerberos authentication guide for a friendly intro to the world of Kerberos.
8 common Kerberos attacks explained
Roasting attacks
There are two main forms of roasting attacks: AS-REQ Roasting & Kerberoasting.
1. AS-REQ Roasting
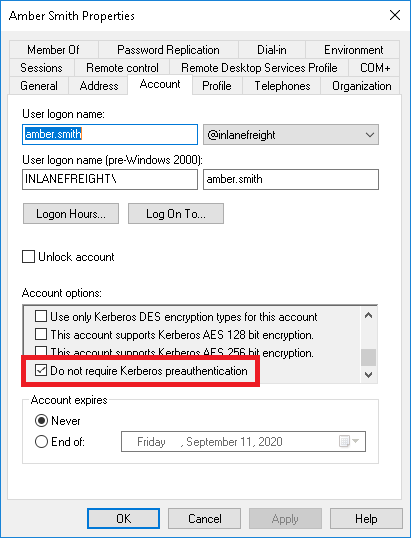
AS-REQ Roasting is possible when Kerberos pre-authentication is not configured. This allows anyone to request authentication data for a user. In return, the KDC would provide an AS-REP message.
Since part of that message is encrypted using the user’s password, it is possible to perform an offline brute-force attack to try and retrieve the user's password.
The only information an attacker requires is the username they want to attack, which can also be found using other enumeration techniques.
If an account has pre-authentication disabled, an attacker can obtain an encrypted Ticket Granting Ticket (TGT) for the affected account without any prior authentication. These tickets are vulnerable to offline password attacks using a tool like Hashcat or John the Ripper.
So, in a nutshell, it's possible to obtain the TGT for any account that has the "Do not require Kerberos preauthentication" setting enabled.
How to mitigate Kerberos attacks
We can harden our organization’s environment against these common Kerberos attacks. Here are some common mitigations you can quickly implement:
-
AS-REP Hardening: Don't set users with Kerberos pre-authentication disabled, and protect accounts with strong passwords.
-
Kerberoasting: use long and complex passwords whilst limiting privileges of serviced accounts.
-
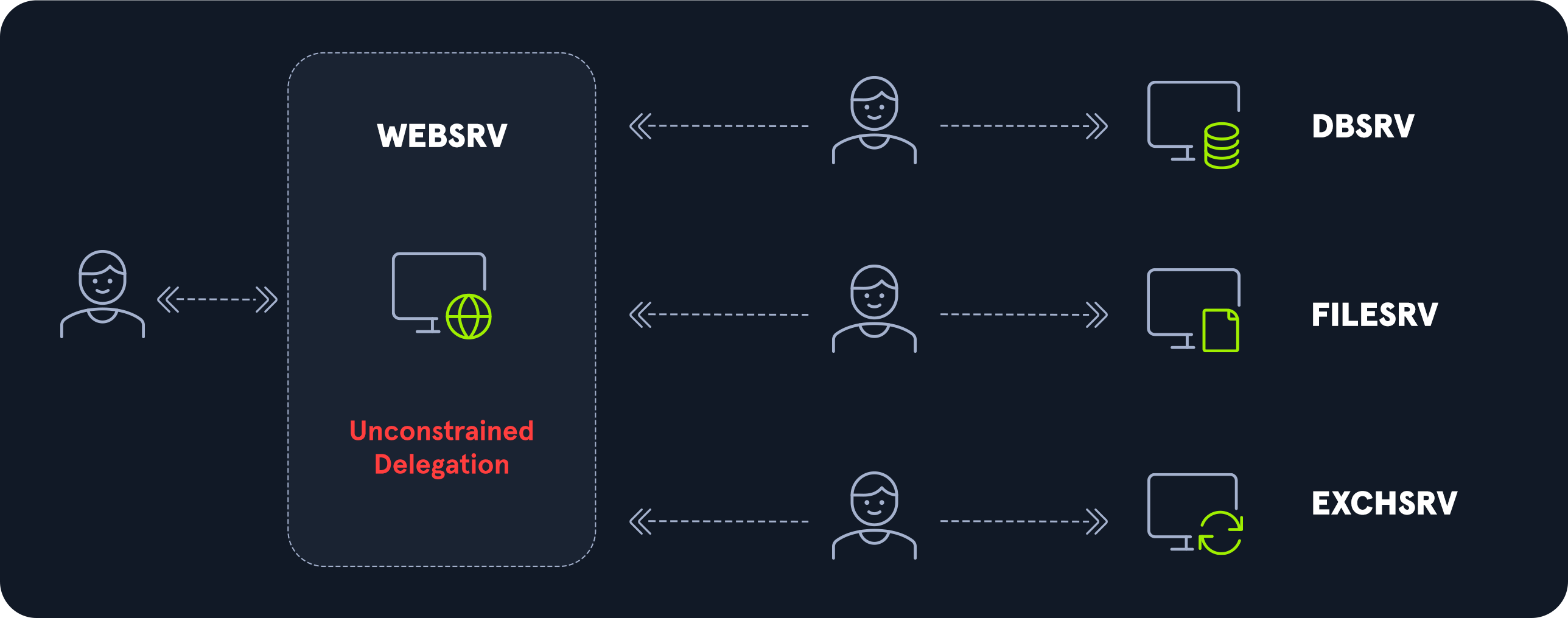
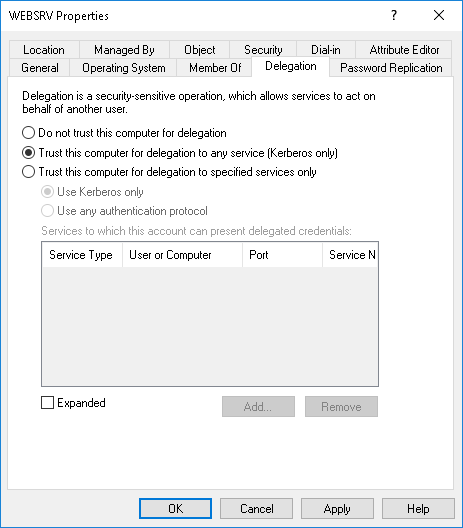
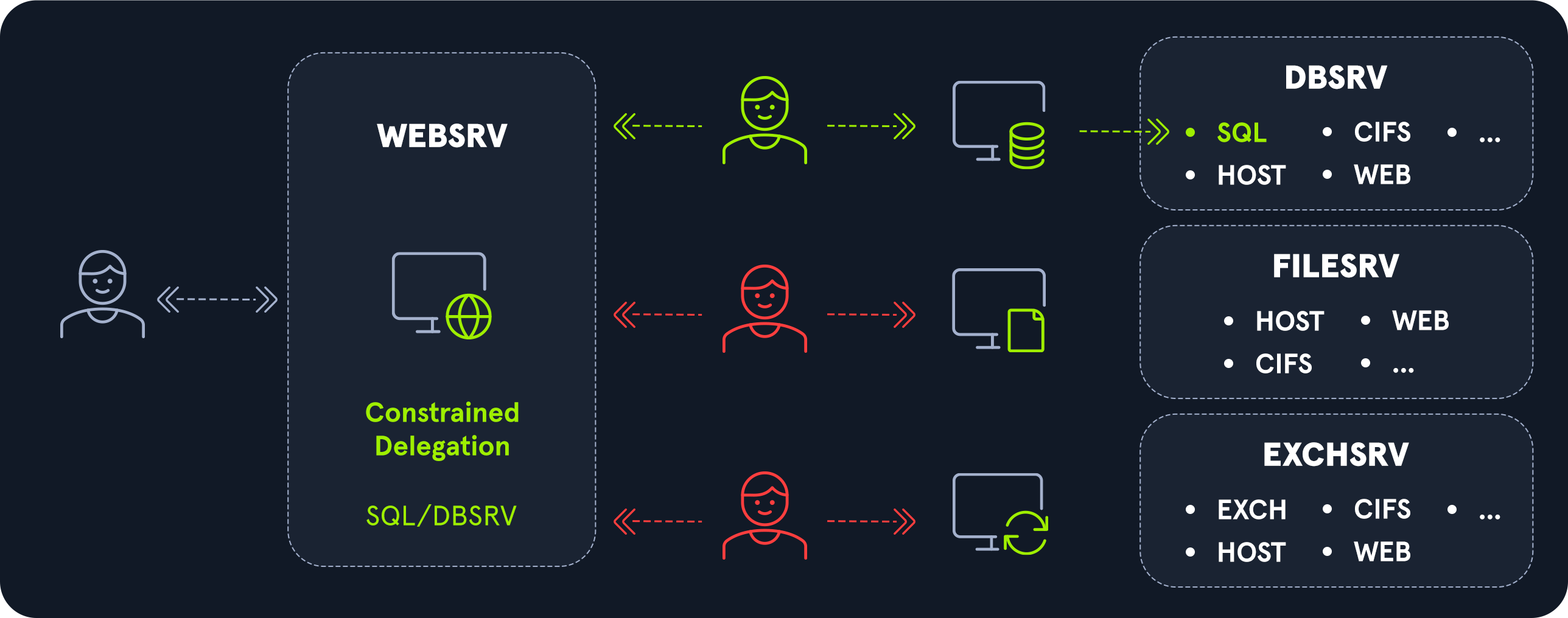
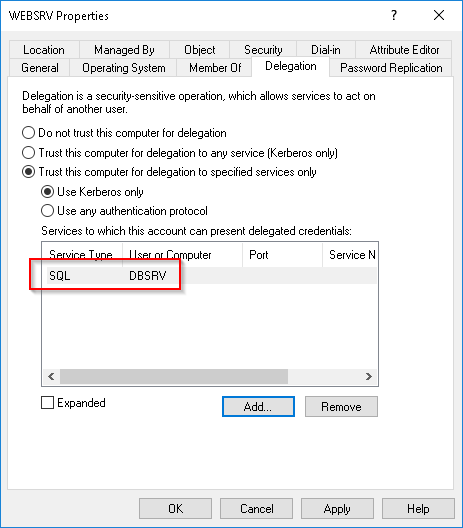
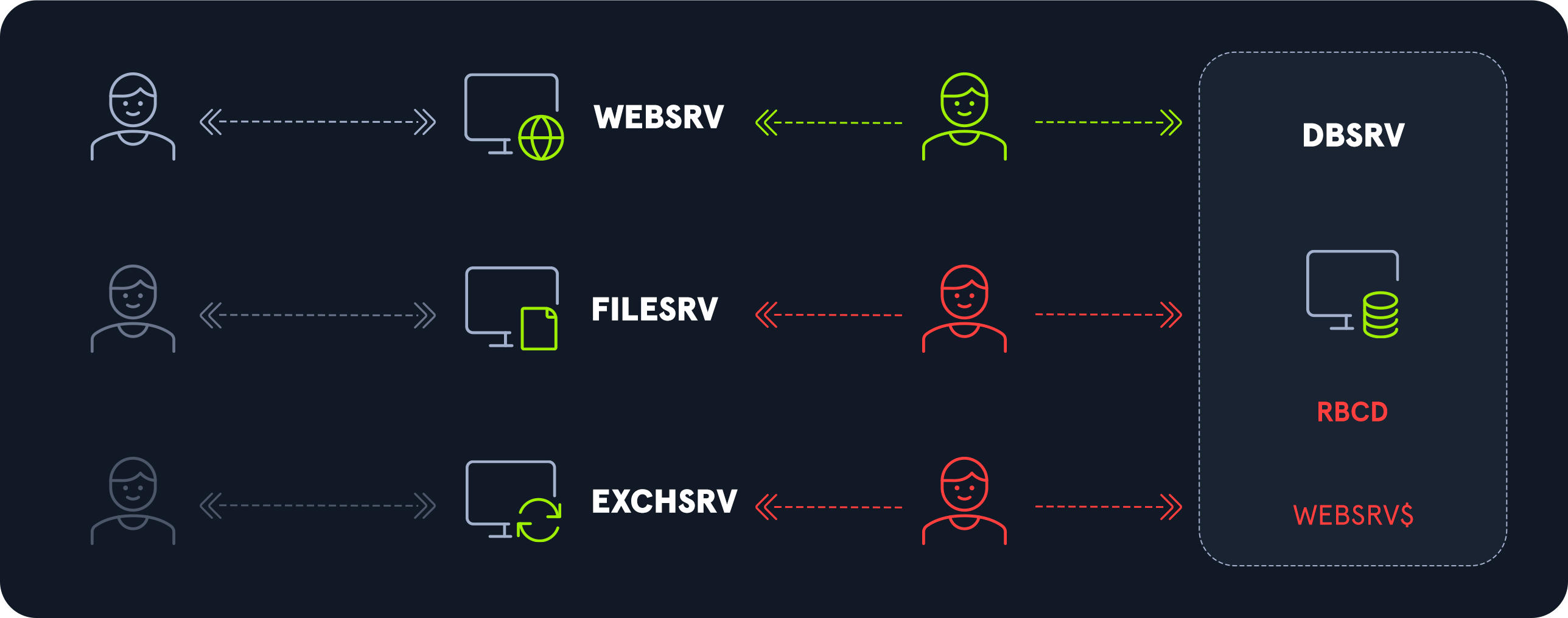
Delegation abuse: disable unconstrained delegation and place users into the Protected Users Group where possible.
-
Golden ticket: limit the number of admin accounts and utilize Multi-factor authentication.
-
Silver ticket: ensure service accounts have strong passwords with a complexity of 25 or more characters and rotate regularly.
-
Pass-the-Ticket: closely monitor events and check any users requesting new TGTs or TGSs outside of normal operations.
Learn how to perform (& defend against) Kerberos attacks
With Kerberos being the default authentication protocol, we must know how to test for vulnerabilities and execute these common attacks.
Our Academy module provides an in-depth study of the Kerberos protocol and its authentication process within an Active Directory network. Practice the most common attacks and upskill so you can protect the authentication process.
|
Author bio: Dimitrios Bougioukas (Dimitris), Senior Director of IT Security Training Services, Hack The Box Dimitrios has extensive experience in upskilling the IT security teams of Fortune 100/500 tech companies and government organizations. He enjoys analyzing the threat landscape as well as interpreting market and data analytics to assist Hack The Box in devising its training strategy and roadmaps, from go-to-market all the way to the syllabus level. Prior to Hack The Box, Dimitrios directed the development of training and certifications through eLearnSecurity/INE and was behind certifications like eCPTX, eWPT, and eCIR. You can connect with him on LinkedIn here. |