Building new skill sets for NIST CSF 2.0
Learn what’s new with the recent NIST CSF 2.0 update and how to build your team’s capabilities to stay compliant with new standards.
Table of Contents
The NIST CSF is a cybersecurity standard that has been successful beyond all expectations. Originally published in 2014 to guide U.S. critical infrastructure cybersecurity programs, it has since been adopted by companies across all industry verticals.
In February 2024, NIST published an updated major version of the standard for the first time in a decade (the previous update, version 1.1, occurred in 2018).
The NIST CSF 2.0 has a new name, an enhanced focus on cybersecurity governance, and guidance on addressing modern cybersecurity threats.
What’s new in NIST CSF 2.0?
The update to NIST 2.0 addresses new and emerging threats and seeks to formalize processes for incident and risk management.
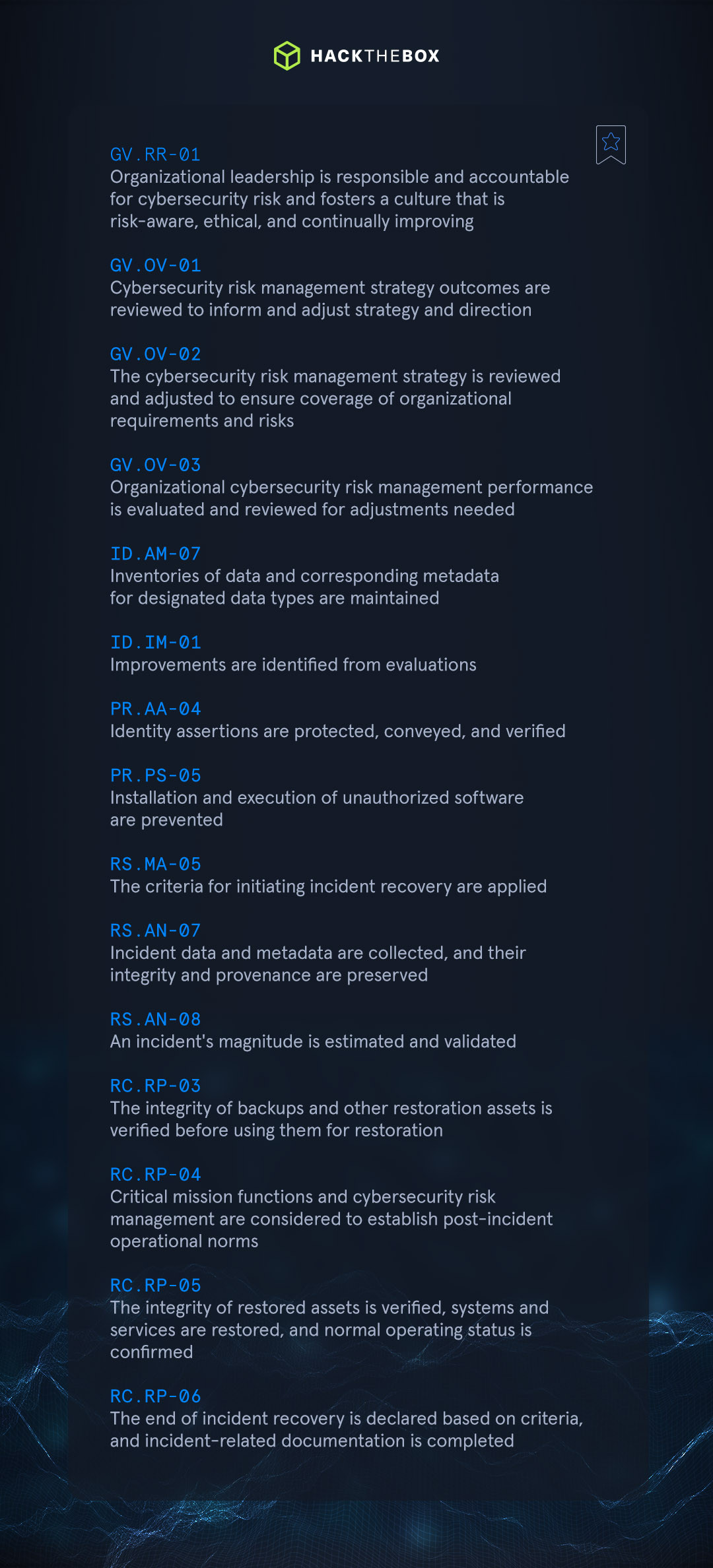
Many changes involve reshuffling existing guidance to create the new Govern core focus. Some organize existing recommendations more logically. Additionally, new sub-requirements are created, including:
-
GV.OV: Results of organization-wide cybersecurity risk management activities and performance are used to inform, improve, and adjust the risk management strategy.
-
PR.PS: The hardware, software (e.g., firmware, operating systems, applications), and services of physical and virtual platforms are managed consistent with the organization's risk strategy to protect their confidentiality, integrity, and availability.
-
PR.IR: Security architectures are managed with the organization's risk strategy to protect asset confidentiality, integrity, and availability, and organizational resilience.
The table below shows the new sub-requirements introduced in version 2.0 of the standard.
Supply chain attacks course
-
Build your org’s ability to defend and detect supply chain attacks with this module.
-
Provides a guided overview of supply chain attacks that cover hardware and software vulnerabilities.
-
Explore the impact of supply chains, the lifecycle of attacks, specific vulnerabilities, and real-world mitigation strategies.
Emerging technologies (like Artificial Intelligence)
Artificial intelligence is a top-of-mind security concern for many, and many jurisdictions are rolling out new regulations, like the EU’s AI Act. NIST has developed an AI RMF to help organizations manage AI risks to their business.
Today, many companies are unaware of how they’re currently using AI and how to manage the associated risks.
Recommended read: How to develop an effective AI risk management strategy.
Learn to defend and exploit AI threats with Dedicated Labs
Our Dedicated Labs track provides insights into common attacks on Artificial intelligence (AI) and Machine Learning (ML) systems, emphasizing underlying principles and demonstrating how insecure implementations may compromise sensitive information or enable unauthorized access.
-
Identify and exploit insecure ML implementations.
-
Exploit classic vulnerabilities through AI systems.
-
Bypass Face Verification Systems.
-
Basic Prompt Injection techniques.
-
Write Machine Learning programs in Python.
-
Privacy attacks on Machine Learning models (white-box and black-box).
-
Train classification models for Membership Inference attacks.
Leveraging NIST CSF & HTB for compliance
The NIST CSF is an optional security standard for most organizations. However, it is also a well-regarded and comprehensive standard that includes crosswalks and mappings to other security standards. Some of the existing crosswalks map to NICE, the CSA Critical Controls, and other major standards.
Regulations are constantly being created and updated to address the latest privacy and security risks (AI, IoT, etc.).
The NIST CSF provides a framework for building an effective and sustainable cybersecurity program, and HTB teaches the skills that employees need to achieve compliance and manage the latest security threats.